Migrating your Microsoft PKI infrastructure to Windows Server 2016 (Part 1)
Migrating your Microsoft PKI infrastructure to Windows Server 2016 (Part 2)
As part of my efforts to upgrade my POC lab to Windows Server 2016 I got around to migrating my PKI infrastructure. This consists of an offline root CA and an online issuing CA. In Part 1 of this guide I will be migrating my offline root CA to Windows Server 2016.
This guide is written as a guide to upgrade from a Windows Server 2012 R2 CA to a Windows Server 2016 CA, however very little has changed since the Windows Server 2003 days and this guide is equally valid for moving a CA from any older version of Windows server to Windows Server 2016.
I am a big advocate of the core versions of Windows Server and in this guide I will be migrating from and to Windows Server core. A CA is a perfect example of a server that does not need the overhead of the GUI and additional services that comes with the full GUI edition of Windows Server and if you don’t already use core for your CA, this is a perfect opportunity to migrate to one!
Preparation
In preparation for the migration build your new Windows Server 2016 server. I recommend that you give it the same name as your current root CA server – it is possible to give it a different name however this will require changing registry keys later on in the migration process. Take this opportunity to patch it with the latest Microsoft patches!
Migration – Backing up your existing root CA server
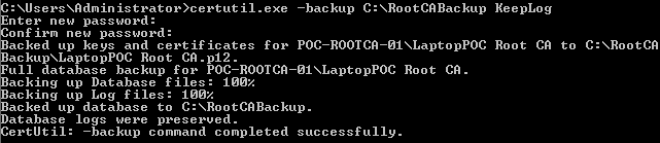
The first step is to back up the CA using the command certutil -backup C:\RootCABackup KeepLog. Note that the KeepLog part is optional, however without it the backup will truncate the logs. I prefer to bring the whole lot across in case the logs are ever needed in the future for auditing purposes.
You will need to enter a password, remember it and make it complex. This backup contains your root CA private key, do not make it easy for an attacker to obtain.
The next thing to backup is the CA configuration, which is stored in the registry in the following location: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\CertSvc. Back it up by typing reg export "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\CertSvc" C:\RootCABackup\CertSvcRegBackup.reg
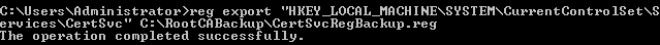
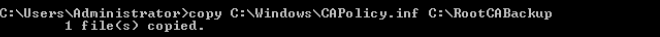
Additionally it is worth backing up your CAPolicy.inf file which you can do easily enough by copying it into the backup folder, by typing copy C:\Windows\CAPolicy.inf C:\RootCABackup
Finally, copy the RootCABackup folder to your new CA.
Migration – Configuring your new root CA and restoring from the backup
Log on to your new root CA server and start by installing the CA role. The easiest way to do this is with PowerShell, so type powershell into your administrative CMD prompt and enter the following command to install the CA role: Add-WindowsFeature ADCS-Cert-Authority
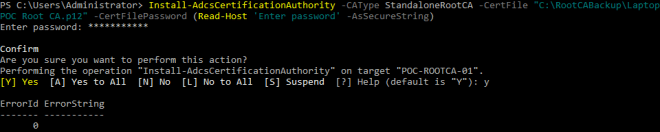
Now configure this new CA using the backup of the old CA. This can also be done with PowerShell using the following command:
Install-AdcsCertificationAuthority -CAType StandaloneRootCA -CertFile "C:\RootCABackup\LaptopPoc Root CA.p12" -CertFilePassword (Read-Host "Enter password" -AsSecureString)
Replace the value after -CertFile with the path and name of the .p12 file from your root CA backup. When you press enter you will be prompted for the password you used to back up your original root CA.
If this step is successful you will receive ErrorID 0 as your return code.
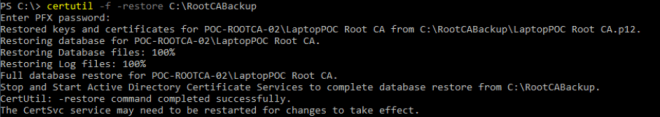
This restores the root CA private key, however next you need to restore the database and logs. Before you do this the CA service must be stopped. Do that by typing in net stop certsvc and pressing enter. Once it has stopped restore the database and logs using the command certutil -f -restore C:\RootCABackup. The -f forces an overwrite of the data that was configured in the barebones CA setup. Once again you must enter the password you used to backup your original root CA.
Do not start the certificate authority service just yet! Before doing that the registry settings from the previous root CA need to be restored. Do this by typing reg import "C:\RootCABackup\CertSvcRegBackup.reg"
Note: If you chose to change the name of your root CA server you will need to go through the values in this registry file and change any reference to the old server name to your new server name before importing it.
Finally copy the CAPolicy.inf file back into the Windows directory by using the command copy C:\RootCABackup\CAPolicy.inf C:\Windows
Now you can start the root CA by typing net start certsvc. The service should start with out any issues. To verify this you should log on to a management workstation and load the Certificate Authority MMC snap-in, connect to the new server and verify that your issued / revoked certificates are listed (as this is a root CA there should be very few issued certificates!)
Once you are satisfied that the new server is configured correctly and working, make sure that you delete the C:\RootCABackup folder. As previously mentioned, this contains your root CA private key, you do not want to leave that laying around!
Coming soon is Part 2, which will focus on migrating the issuing certificate authority. Thankfully the steps for this are very similar with only small differences due to it being a domain joined server.

nice guide, thanks. In case anyone bumps into the same problem I had though, the install-adcscertification command fails if the server has no network adapter, as would often be the case with an offline root CA. Details of the fix here – https://www.sysadmins.lv/blog-en/install-adcscertificationauthority-issue-when-installing-an-offline-certification-authority.aspx
LikeLiked by 1 person
I was considering the use of server core for the various PKI components. I would agree with your approach on using server core for network connected server, managing these from a separate management workstation. I would normally build the root CA as a server that has never been connected to any network, using an unattended build process and USB based image. For this server I see no advantage to using core with the server never connecting or needing to be patched. Just a personal preference mind, but I would prefer the convenience of GUI tools for the root CA.
LikeLike
In article https://social.technet.microsoft.com/wiki/contents/articles/37373.migrating-ad-certificate-services-from-windows-server-2008-to-windows-server-2016.aspx there is stated, that you can’t migrate directly from Windows Server 2008 to Windows Server 2016 due to the JET database engine changes. Is that right? The author recommands to do it in two steps – first migrate to Windows Server 2012 and than migrate to Windows Server 2016. Do you agree?
LikeLike
I just followed these steps for the Issuing CA and moved from 2008 R2 to Server 2016 with just a few minor problems:
1) If your database files are stored on non-default paths, update them in the registry file (someone had moved them to a separate VHD previously)
2) The backup command “certutil -backup C:\RootCABackup KeepLog” wouldnt work properly (database problems, also the reason for the upgrade). I had to run the backup from GUI for a complete backup and then restore
LikeLike
Thanks for the tutorial but i found an issue. When we upgrade from 2012R2 to 2016 we lost all template certificate inside “certAuthority”
For fix it i change the number 5 to number 10 on flags here : CN=Enrollment Services, CN=Public Key Services, CN=Services, CN=Configuration,DC= and the value should be 10 for an Enterprise CA.
Source : https://social.technet.microsoft.com/Forums/ie/en-US/f0f3af84-58c1-459a-98d0-04a39078f1e1/windows-server-2012-r2-cannot-issue-new-certificate-template?forum=winserversecurity
LikeLike
Hi Kevin followed your artical in restoring the CA from 2008R2 to 2019
In the Lab manged to restore the CA following the instructions
https://kevinstreet.co.uk/category/certificate-authority/
But when trying to restart the CA I receive the following error message – File not found 0xc8000713 (ESE:-1811 JET_errFileNotFound)
Any ideas, some resources are stating you have to go from 2008R2 CA > 212CA then to 2019 CA?? but conflicting information online??
Any information would be greatly appreciated??
Kind Regards
John
https://social.technet.microsoft.com/Forums/windowsserver/en-US/f0b24ec3-bec9-4e6b-ad48-5017038252b8/redepoly-ca?forum=winserversecurity#2218bfca-dabb-4717-af56-318520eddbba
LikeLike
I have a question: I don’t have the capolicy.inf in my root ca, why?
and in my sub ca the file is commented in the extension with .txt
what is this file for? what happens if i rename the file in sub ca correctly? i found it already like this.
many thanks,
LikeLike