Each release of SCCM current branch has been improving how it manages Office 365 clients, and the last couple of versions have improved the user experience the most. The only real issue remaining is that, under certain circumstances, the user will be prompted to reboot once the Office 365 update is complete. This reboot is not actually necessary, however. Here is how to go about setting up SCCM so that it delivers Office 365 updates to users without prompting them for an unnecessary reboot.
For starters, make sure your SCCM environment is syncing Office 365 client updates. To do this open the SCCM console and navigate to Administration > Site Configuration > Sites, select your site and select Configure Site Components > Software Update Point. Click on the Products tab and make sure Office 365 Client is ticked. Click OK to close that dialog and then head over to Software Library > Software Updates > All Software Updates and select Synchronize Software Updates in the ribbon.
Another thing to check is that the Office 365 client agent on users’ machines is configured to be managed by SCCM. You can set this in the Client Settings of SCCM. Go to Administration > Client Settings and click properties on the device settings policy your clients receive. Select Software Updates and ensure that Enable management of the Office 365 Client Agent is set to Yes.

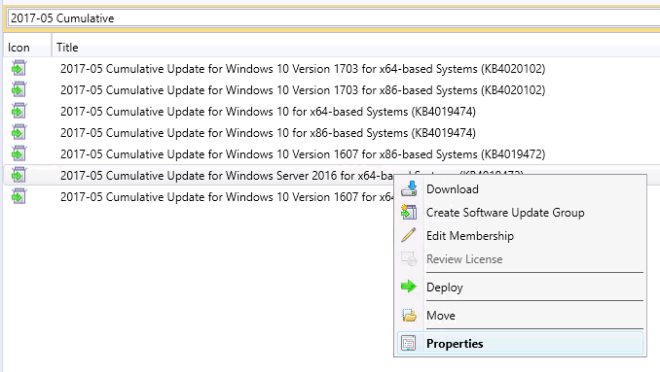
Once that’s had time to process, create an Automatic Deployment Rule to push out the updates each month (or on whatever schedule you prefer). Under Software Updates go to Automatic Deployment Rules and click Create Automatic Deployment Rule. Give it a name, such as Office 365 Monthly Updates, and select the target collection that contains your clients that need updating. Click Next, and Next again and now select the criteria for updates in the ADR.
Select the following options:
Date Released or Revised: Last 1 month
Product: Office 365 Client
Superseded: No
Title: -semi-annual OR -Monthly Channel (Targeted)
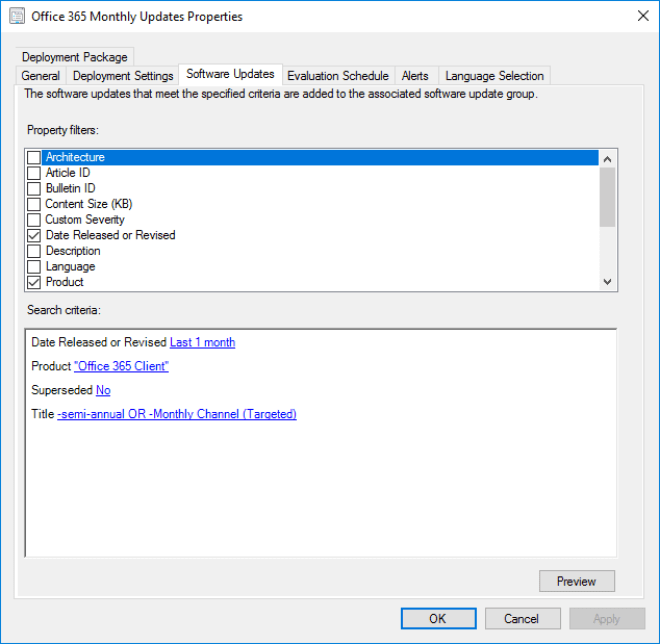
Those two items in the Title field (-semi-annual and -Monthly Channel (Targeted)) means exclude any updates with ‘semi-annual’ or ‘Monthly Channel (Targeted)’ in the name. This is because I only want the Monthly Channel updates in my ADR. If you prefer to get the semi-annual updates in yours, do not add that and add ‘-Monthly Channel Version’ to your title instead.
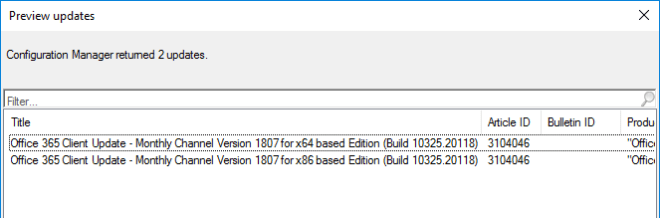
Click Preview to ensure you’re getting what you expect. If not, the updates may not have synchronized yet.
Click Next and select the schedule you want this ADR to evaluate on. Office 365 client updates are released every month (for monthly channel) but not on any particular day, so I have this rule run toward the end of each month to hopefully catch that month’s client update.

Click Next and select when you want these updates to be pushed to users. This will depend on your organisations patching schedules and agreements, however I set both the available time and deadline to As soon as possible. This is because I want these updates to be delivered to users as soon as their SCCM client receives the notification of the update.
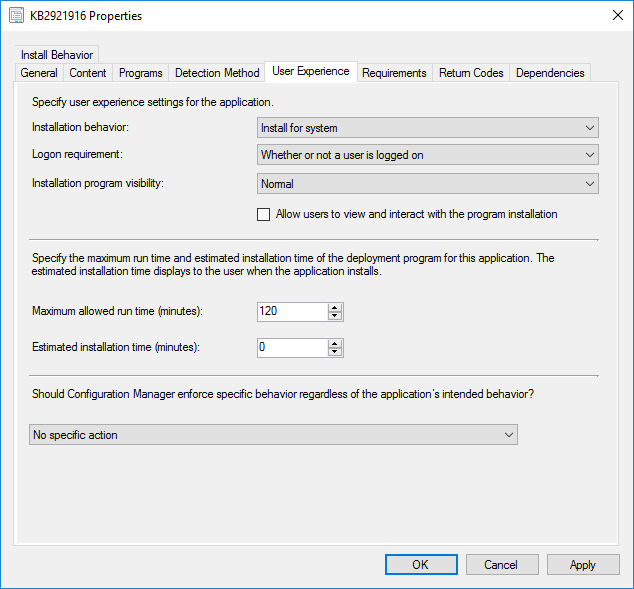
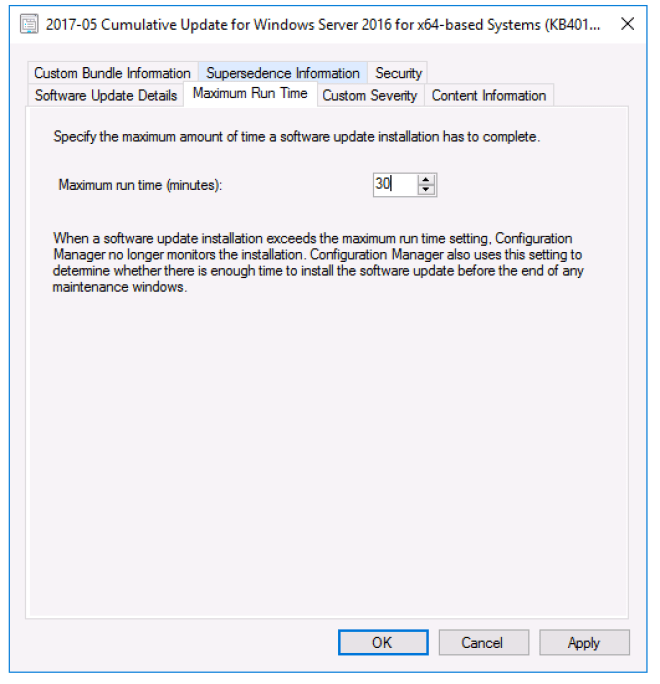
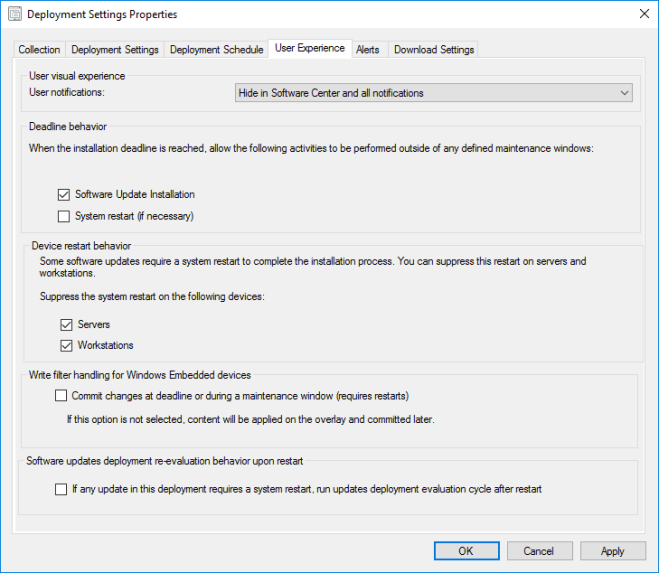
On the next screen, this is where you need to select specific options to get what I consider to be the best user experience for the Office 365 client updates. In User notifications select Hide in Software Center and all notifications. Under Deadline behaviour tick Software Update Installation, and under Device restart behaviour tick to suppress updates on both Servers and Workstations.
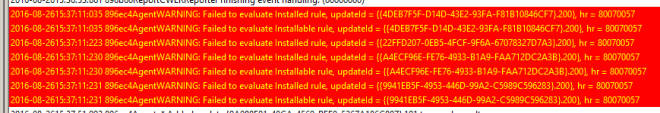
Okay, time for a tangent to explain how this is beneficial to the Office 365 update user experience. If you select Display in Software Center for the user experience and omit the system restart suppression the user will be notified that new updates are available. If they go to Software Center, find the update and click Install they will be presented with the following dialog:

As it suggests, when they click Install any Office applications they have open will close and the user will think they need to wait for the update to complete before they can continue to work. On top of that, when the update does complete, it will prompt the user to reboot their PC.
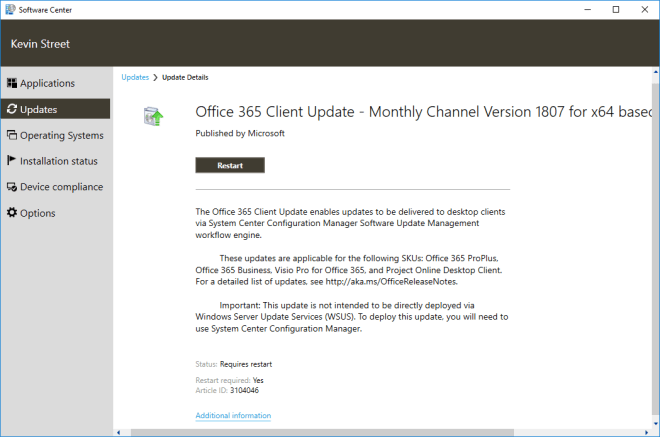
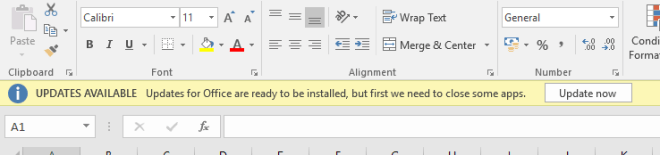
The problem is that the user waiting, and rebooting are a waste of their time. Office is able to install updates in the background while the user is working and only actually needs the user to close the apps right at the end of the install to complete the update. Office prompts the user to complete this step by means of a banner that appears in any of the Office apps that the user opens after the update has finished doing what it can. They can then click Update now at their leisure, and because most of the update process has taken place behind the scenes, the users’ downtime is only a few minutes. Office will even re-open the apps the user had open when it is complete!
So, to mitigate this sub-par user experience, the deployment settings for the ADR should be set to Hide in Software Center and all notifications, with the update allowed to install once the deadline is reached and all restarts supressed. From the users’ point of view, they will not see any indication that Office is being updated until they see the banner in their app prompting them to Update now. They can ignore this until a time that suits them, or it can just happen at the end of the day when they shut down their machine and pack up for the day. And better still, no unnecessary restart prompt.
Let’s get back to that ADR, there isn’t much left to do. Click Next and Next again to get to the Deployment Package page. Create a new deployment package (or add to an existing one, if you wish) and click Next. Continue through the ADR wizard, selecting the download location and which languages you wish to download and finally complete the wizard. Select your new ADR and click Run Now in the ribbon to get the Deployment Package and Software Update Group created. Be aware that this will also create the deployment to the client collection you selected at the start of the process, so make sure that’s acceptable! If it’s not, you may wish to change the deployment collection to a collection containing test clients or just your own machine at first to test that the user experience is what you expect it to be.
And that’s it! Office 365 client updates deployed to your users in the best possible way.