Installing Remote Server Administration Tools (RSAT) for Windows 10 1809 (including SCCM deployment) (Part 1)
Installing Remote Server Administration Tools (RSAT) for Windows 10 1809 (including SCCM deployment) (Part 2)
In the first part of this guide I stated that in order to install RSAT in Windows 10 1809 and above, Windows needs to be able to reach the Internet to download the source files. This is due to RSAT being a feature-on-demand in 1809 and above, so the files are not included on the disk but instead hosted online and downloaded when required.
Well it turns out the source files can be downloaded, if you have access to Microsoft Volume Licensing Service Center or Visual Studio downloads. Search for “features on demand” and make sure you download the latest ones for 1809 (in my Visual Studio downloads portal it is listed as “Windows 10 Features on Demand, version 1809 (Updated Sept 2018)”).
Once you have downloaded the ISO, you can use it as the source location when installing RSAT with PowerShell. Say, for example, you mount the ISO as the F: drive, you would use the following command:
Get-WindowsCapability -Online | Where-Object {($_.State -notmatch 'Installed') -and ($_.Name -match 'RSAT')} | %{Add-WindowsCapability -Online -LimitAccess -Name $_.Name -Source F:\ }
However, there is a lot more on that disk than just the files required for RSAT, and if you wish to use this in an SCCM package you will want to sanitise it a bit. The whole disk contains 4.6 GB of files, however the ones we need for RSAT are only about 500 MB.
To create a package using only the files you need for RSAT, create a folder somewhere called RSATSource and copy the files with the following names (there will be multiple files per search, you need all of them):
Microsoft-Windows-ActiveDirectory-DS-LDS-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-BitLocker-Recovery-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-CertificateServices-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-DHCP-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-DNS-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-FailoverCluster-Management-Tools-FOD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-FileServices-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-GroupPolicy-Management-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-IPAM-Client-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-LLDP-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-NetworkController-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-NetworkLoadBalancing-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-RemoteAccess-Management-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-RemoteDesktop-Services-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-ServerManager-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-Shielded-VM-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-StorageMigrationService-Management-Tools-FOD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-StorageReplica-Tools-FoD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-SystemInsights-Management-Tools-FOD-Package~31bf3856ad364e35~amd64~Microsoft-Windows-VolumeActivation-Tools-FoD-Package~31bf3856ad364e35~amd64~
You will also need to copy the “metadata” folder and the file “FoDMetadata_Client.cab”. With these files copied into their own folder, you can change the PowerShell to:
Get-WindowsCapability -Online | Where-Object {($_.State -notmatch 'Installed') -and ($_.Name -match 'RSAT')} | %{Add-WindowsCapability -Online -LimitAccess -Name $_.Name -Source C:\RSATSource }
Obviously replace C:\RSATSource with the location of the source folder you copied all those files into.
Creating an SCCM application to deploy RSAT
Since I already wrote this up in Part 1 of this guide, this part is mostly just a rehash of that. However, there is one change to the script so that it now uses the local packaged source, rather than going online to download the source.
To create an application in SCCM you will need three things: An install command, an uninstall command and a detection method. To cover the install and uninstall command, let’s create a PowerShell script with an install and uninstall function that can be called from the command line. The following PowerShell script is used to install and uninstall all RSAT components; if you want to pick and choose the ones you install or uninstall, modify it accordingly.
## Install all RSAT components
Function InstallRSAT {
Get-WindowsCapability -Online | Where-Object {($_.State -notmatch 'Installed') -and ($_.Name -match 'RSAT')} | %{Add-WindowsCapability -Online -LimitAccess -Name $_.Name -Source $PSScriptRoot\RSATSource}
}
## Uninstall each RSAT component so that no dependancies are left behind
Function UninstallRSAT {
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.BitLocker.Recovery.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.CertificateServices.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.DHCP.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.Dns.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.FailoverCluster.Management.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.FileServices.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.IPAM.Client.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.LLDP.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.NetworkController.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.NetworkLoadBalancing.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.RemoteAccess.Management.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.RemoteDesktop.Services.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.Shielded.VM.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.StorageMigrationService.Management.Tools')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.StorageReplica.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.SystemInsights.Management.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.VolumeActivation.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.WSUS.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.ActiveDirectory.DS-LDS.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.GroupPolicy.Management.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
Get-WindowsCapability -Online | Where-Object {($_.State -match 'Installed') -and ($_.Name -match 'Rsat.ServerManager.Tools~~~~0.0.1.0')} | %{Remove-WindowsCapability -Name $_.Name -Online}
}
## Get the parameter passed to the script
$DeploymentType=$args[0]
## Run the install or uninstall function
if ($DeploymentType -eq "Uninstall") {
UninstallRSAT
}
else {
InstallRSAT
}
Copy that script and save it as Install-RSAT.ps1. Create your application in SCCM and go through the wizard, giving it a name, publisher and version. The source will be the location where you saved Install-RSAT.ps1. Don’t forget to also copy your RSATSource folder to this location! When you get to the install and uninstall commands in the wizard, you can use the following commands:
To install:powershell.exe -ExecutionPolicy Bypass -File .\Install-RSAT.ps1 -DeploymentType Install
To uninstall:powershell.exe -ExecutionPolicy Bypass -File .\Install-RSAT.ps1 -DeploymentType Uninstall
Next up is the detection method. For this, you will need to use a PowerShell detection method. The PowerShell will simply check that the RSAT optional components have their install state set to Installed:
$installed = Get-WindowsCapability -Online | where name -like RSAT* | where state -like Installed | select name
if ($installed) {
return $true
}
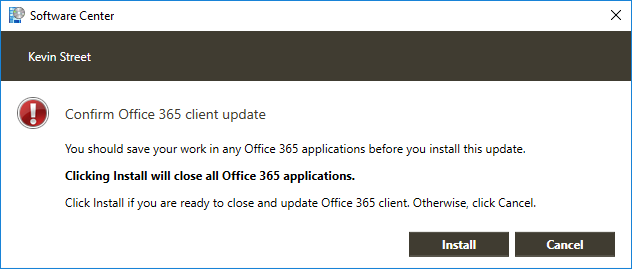
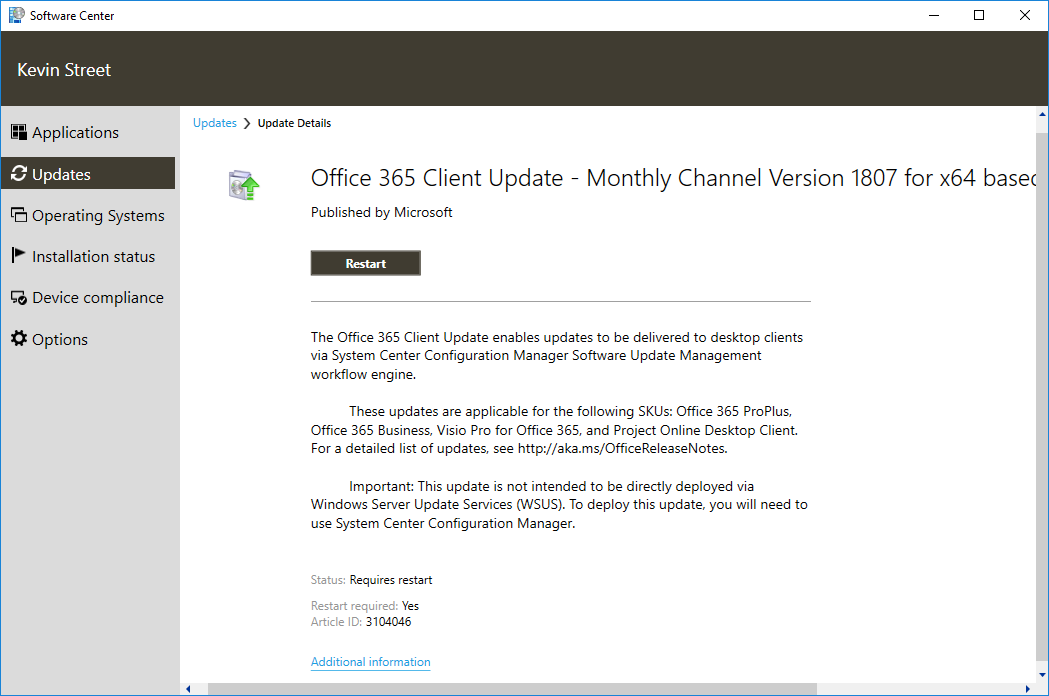
That should be all you need! Deploy that to a Windows 10 1809 device and the user should be able to install RSAT from Software Center.